
Cybersecurity has moved beyond firewalls to become a matter of enterprise-wide capital allocation and board-level strategy. Yet the perception of the CISO as a technical guardian persists across many organizations, even as the role has expanded to touch capital decisions, operational resilience, and enterprise governance at the highest levels. The gap between how the role is understood and what it actually demands is where many organizations are most exposed.
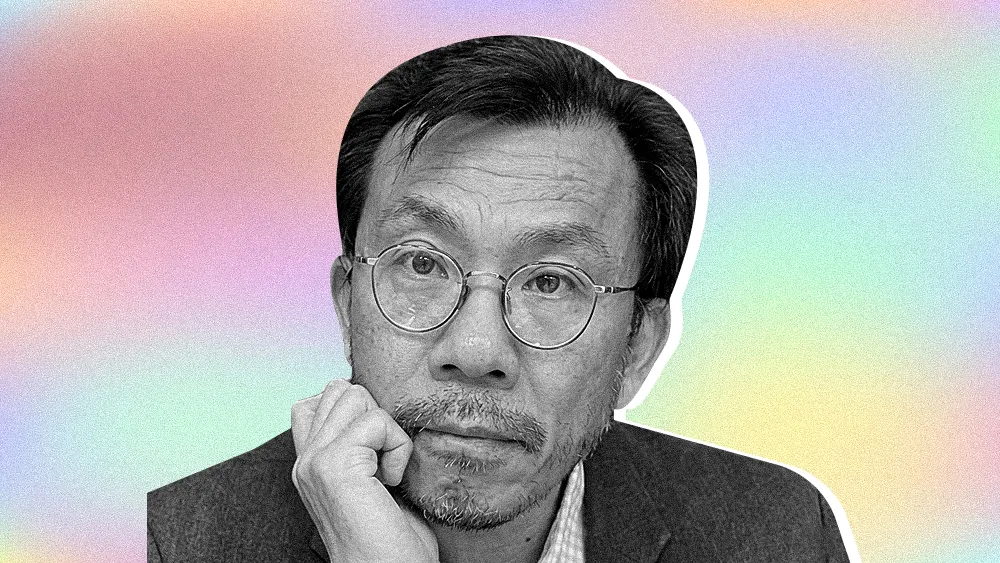
Masato Yamanishi is the SVP and Global CISO at Olympus Corporation, a global medical technology company. With over 19 years of experience leading IT and security for global enterprises, including security strategy roles at Nissan Motor Corporation and Santen Pharmaceutical, Yamanishi brings a clear conviction to his current role: that organizations need to adopt a new model of security leadership that is inseparable from business strategy.
“Ninety percent of my time is spent on business matters, like business continuity, risk visualization, shadow IT exposure, and explaining impact to top management. It’s not spent on technical controls," said Yamanishi. As the role has expanded, the modern CISO has had to evolve into a translator and risk communicator.
That business-first mindset often stems from fundamental disconnects in how many organizations manage cyber risk. The inclusion of cybersecurity in Enterprise Risk Management (ERM) frameworks frequently fails to translate awareness into action. Yamanishi sees this playing out at two levels: in how organizations assess the likelihood of a cyber event, and in how that assessment flows through to budget decisions even when the risk rating is high.
A tale of two budgets: For Yamanishi, effective risk management requires clarity about which conversation you are having. "Risk needs to be viewed in two layers. The higher layer is deciding budget allocation between security and other critical matters," said Yamanishi. "The second layer is how to allocate the budget within security among various security initiatives." At the second tier in particular, he observed, risk management principles are often absent entirely, with decisions made on instinct rather than structured prioritization.
A risk of certainty: That underestimation has real consequences. "With other risks, you can say an event 'may or may not happen.' But in the case of cyber, it will happen in the near future," said Yamanishi. "I'm afraid that this very high likelihood is underestimated. Even when cyber risk is evaluated highly, it's not reflected in the budget allocation. That's the other gap I'm seeing." The problem, as he describes it, is not a lack of awareness but a failure to let that awareness change behavior.
Yamanishi explained that being a strategic enabler is difficult without the right structural authority, noting that a CISO's position in the organizational chart is a key part of strategic alignment. The reporting line powerfully shapes how the entire company perceives the security function. His point speaks to a broader trend of the CISO's expanding influence, where positional power is needed to drive change. With a career that serves as a case study in organizational politics, he has seen firsthand how misalignment can reduce security to a tactical problem, diminishing its strategic influence.
A tale of three bosses: Yamanishi has held three distinct reporting lines across his career, and each one sent a different signal to the organization. "My experience has shown me how much the reporting line defines the security function. When I reported to the CIO, people perceived security as purely an IT matter," said Yamanishi. "Under a Chief Administrative Officer, it was correctly seen as a corporate function. But when reporting to the General Counsel, people tend to believe security is just a part of compliance, and they try to minimize its mandate." The right reporting line, as he sees it, is not simply an organizational preference. It is a strategic decision that determines how much authority the CISO can actually exercise.
To address these shortcomings, Yamanishi's approach is to reposition how the CISO role drives business growth, drawing on security leadership strategies that challenge conventional assumptions about where governance ends and growth begins.
Permission to innovate: For Yamanishi, the tension between innovation and governance is a false one. "Many people misunderstand innovation and governance as being different things. In my view, governance is actually a part of innovation, requiring new approaches like AI-native security," said Yamanishi. "I recently found a very good phrase for this: Security is a growth enabler. Without investing in security, growth and innovation will be slowed down or prevented, so the two cannot be separated." It is a framing that repositions the CISO not as a constraint on the business but as one of its core drivers.
Speaking the board's language: Communicating this philosophy effectively often requires a new strategy. "When IT teams explain things with too much technical detail, management often cannot understand the core issue. While they know it's important, the lack of understanding leads them to delegate the responsibility away instead of owning the risk," said Yamanishi. His solution is to meet the board on its own terms. "When I speak to the board, I focus on the business impact of a cyberattack and the required investment. I talk about technology a very small percentage of the time, maybe less than 10 percent," he explained. "The main portion of the explanation must be about business impact."
When it comes to translating strategy into execution, Yamanishi is candid about the ongoing challenges. At a global manufacturer like Olympus, for example, that includes involving everyone from R&D to sales, not just the security team alone.
Whose BCP is it anyway?: The challenge, as Yamanishi sees it, is one of ownership. "To avoid business impact, every important asset needs a Business Continuity Plan. But that BCP must be developed by the owner of that business process or operation," said Yamanishi. "It should not be developed by IT, and not by the security team. This is why involving various functions is so important. They must own their own resilience." For the security team, he noted, the role is to drive that conversation, not to write the plan on everyone else's behalf.
The evolution Yamanishi describes cannot succeed without corresponding changes at the top of the governance structure. Many organizations claim to have board members with sufficient cyber expertise, but most have legal backgrounds alone. While valuable, this does not provide the technical grounding needed to meaningfully oversee security risk. The gap, as he sees it, extends beyond the boardroom. It starts with how the industry develops its security leaders.
"The industry's training and education programs are another gap. In my view, they focus too much on technical matters. Even the CISSP certification has some governance, but it is still 80% technical," said Yamanishi. "This is not the curriculum we need to develop effective board members or even modern CISOs."
.svg)