For years, the tension between a company's tech and security leaders played out as a turf war: delivery versus protection, speed versus caution. That framing no longer holds. As AI adoption, regulatory pressure, and evolving threats pile new responsibilities onto both roles, the old question of who reports to whom is giving way to a more urgent one: how do two leaders with fundamentally different mandates build an enterprise that can deliver and defend at the same time? With boards and customers now judging security failures and delivery failures with equal severity, the CIO-CISO relationship is becoming one of the most strategically consequential partnerships in the enterprise. Getting it right is no longer optional.
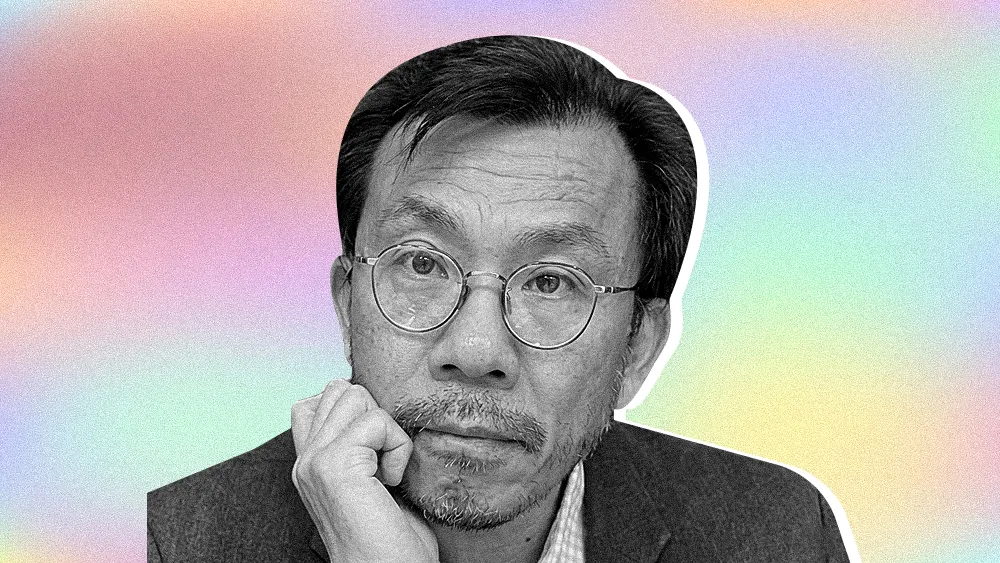
Few people understand this pressure-cooker relationship better than Ann Dunkin. With a 360-degree view forged as CIO for the U.S. Department of Energy and EPA, CIO of Santa Clara County, and executive roles at Hewlett Packard and Dell, Dunkin is now a Distinguished Professor at Georgia Tech focusing on technology leadership and AI, through groups like CGAI. She also serves on corporate boards including the Global Interconnection Group, advising on energy infrastructure and emerging technology. The author of Industrial Digital Transformation, she has seen the CIO-CISO dynamic succeed and fail across every sector, and believes the difference rarely comes down to org charts.
"If the CIO and the CISO aren't successful together, neither one of them is successful. It's because security failures and delivery failures are judged the same way by the organization," said Dunkin. That shared exposure shapes how she thinks about the relationship from the ground up. In her experience, the CIO who understands they are ultimately on the hook for security outcomes is the one most likely to invest in making the partnership work.
According to Dunkin, the relationship is often fraught from the start, but not because of org charts. While many companies get bogged down in debates over reporting structures and other forms of organizational design, that focus misses the point. The friction typically emerges from a classic clash of duties.
The department of no: "CISOs must respect that the CIO's job is to get something done, and CIOs must respect that the CISO's job is to secure the enterprise. Without that mutual respect, the CISO can become the 'department of no,'" said Dunkin. "Or, on the other side, the CIO runs roughshod over the security agenda as the 'department of yes,' saying yes to everything." The stakes of getting that balance wrong fall disproportionately on one side, and in most organizations, when something goes wrong, it is the CIO who answers for it, she noted.
One neck to choke: That relationship is also shaped by pressures from the top. A fight for a "seat at the table" can create tension, as strategic communication gaps often exist between boards and security leaders with their expanding responsibilities. As the CISO's role in the boardroom has grown, the conversation has sharpened its focus on ultimate accountability, a trend backed by research on CISO-board dynamics. Such accountability can be a powerful force for alignment, cementing cybersecurity as a core business function. "In the federal government, the law dictates that CISOs report to CIOs, and Congress generally looks at the CIO as the neck to choke. That clear line of accountability runs directly to the CIO, which forces them to be security-minded because they are ultimately on the hook for failure," said Dunkin.
When that alignment fails, the result is often a costly pattern Dunkin calls "enterprise task-switching." The problem is fueled by a constant stream of external pressures: the CIO wants to implement AI while the CISO battles AI-enabled attacks, or both face intense competition for limited budgets. According to Dunkin, the consequences of this internal friction are predictable and wasteful.
Guardrail to guardrail: "I worked with one tech company that prided themselves on going 'guardrail to guardrail,' which meant one week we're doing this, and the next week we're doing that. They just drove their staff nuts," said Dunkin. The pattern, she observed, is not merely disruptive. It signals something deeper about whether leadership has a clear destination.
"I worked at one tech company that prided themselves on going 'guardrail to guardrail,' which meant one week we're doing this, and the next week we're doing that. They just drove their sales force nuts," said Dunkin. The pattern, she observed, is not merely disruptive. It signals something deeper about whether leadership has a clear destination.
The project that never was: "I worked with a different company where we attempted to build the same product five times," she continued. "We kept stopping and starting. In the time frame, and with the resources we spent, we could have probably built it two or three times over." The cost was not just time, she noted. The repeated restarts consumed the same resources that could have delivered the product outright.
The chaos tax: "Constantly changing direction is a sign of leadership that doesn't know where it's going. That indecisiveness costs you money and time, but more importantly, it costs you the goodwill of your employees. Eventually, they assume you don't know what you're doing, or you simply don't care that you're sending them into chaos all the time." The distinction she draws is between necessary pivots and directionless churn, and she said the latter is always visible to the people being asked to absorb it.
Dunkin identified a disciplined framework for managing capacity as the practical foundation for CIO-CISO alignment. Under this model, leaders structure their teams to operate in three modes at once: long-term projects, daily operations, and a dedicated response function. Such a structure provides boards with meaningful risk signals that reflect mature governance as a shared responsibility. "You basically need three modes to operate in. You have your long-term strategic projects and your day-to-day operational work, but those two things can't add up to 100% of your capacity," said Dunkin. "You have to save capacity for the incoming threats and opportunities so you aren't forced to drop everything and create chaos."
That investment in the core relationship creates a foundation that cascades through the entire organization. It’s a fundamental commitment to a unified front. "In a perfect world, your CIO and CISO act like they're best friends. They may not like each other at all, but they operate like the best of friends," said Dunkin. "When they are constantly in alignment, their teams see it, the organization sees it, and good things happen."
.svg)