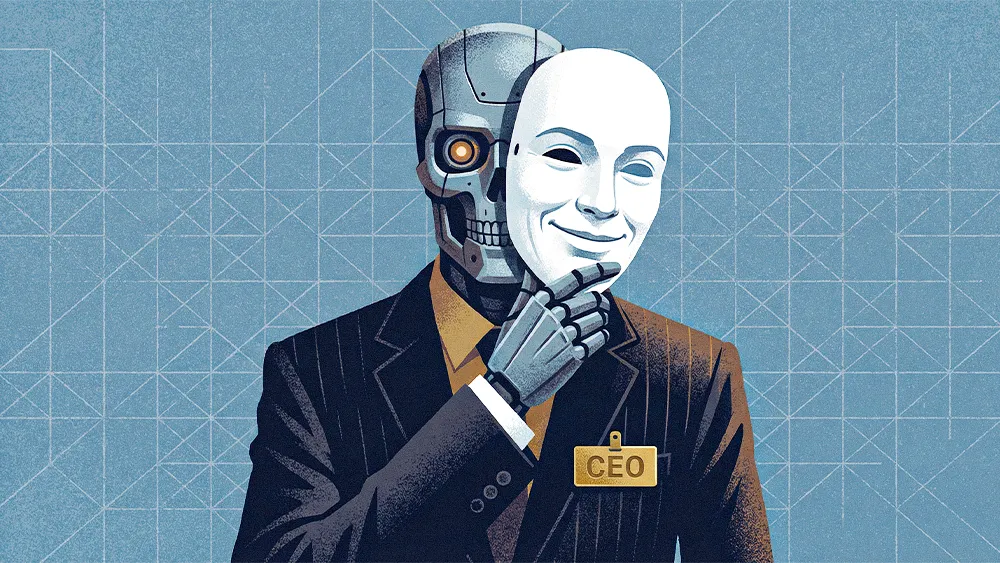

Cybersecurity’s frontline has moved straight into human decision-making. Modern attackers use AI to craft flawless, hyper-personalized messages that mimic colleagues, executives, and trusted partners through text, voice, and video. These tactics render old warning signs meaningless and expose a deeper weakness inside organizations. Breakdowns happen when pressure and convenience short-circuit established processes, allowing deception to succeed without ever touching a firewall.
Amit Basu is Vice President, CIO, and CISO for International Seaways, one of the world’s largest energy transportation companies, with more than 30 years of global experience across IT and cybersecurity. He leads the company’s digital transformation and enterprise cyber resilience efforts and serves on cybersecurity advisory boards at Pace University and Ithaca College. As a Founding Member of the Professional Association of CISOs, Basu operates at the intersection of academic thinking and operational risk, where security theory is constantly tested by real-world pressure.
"It’s often convenience and complacency that cost us, not a lack of technology. It's not enough to trust what we see or hear; it has to be substantial proof," Basu said. Under pressure, employees defer to urgency and authority, bypassing verification steps designed to protect the business. When that happens, even mature security programs fail, leaving organizations exposed to attacks that succeed through persuasion rather than technical force.
The urgency illusion: "Fake urgency, like quarter-end pressures, drives mistakes. These sham urgencies need to go, and employees who question unusual requests should be encouraged," Basu said. Creating a culture where employees feel safe to flag unusual requests is critical to preventing costly errors.
Identity crisis: Many high-profile breaches trace back to skipped procedures rather than missing tools, Basu said, pointing to a widely reported case where finance executives transferred more than $20 million after a deepfake call that a simple callback verification could have stopped. "The danger is assuming identity has already been proven. People believe multifactor authentication will always work, but as identity becomes the primary attack surface, that kind of trust creates blind spots attackers are quick to exploit."
Trust issues: "Every time I do something unusual, the system should ask me again," he continued, describing approaches like adaptive authentication and continuous verification. "The system can challenge you differently depending on where you’re logging in from, the time of access, or the resources you’re trying to reach." For high-risk actions, he advocated layered, out-of-band confirmation, such as a phone call or secondary approval, to ensure the request is legitimate.
.svg)