Data exposure is no longer the only concern. Agents take action, and they do it at scale.

In the last six months, a new class of tools has entered the enterprise, as non-human operators capable of taking action across systems. These tools, commonly referred to as persistent AI agents or cowork agents, are designed to run locally or on private servers and can assist employees or act on their behalf. And while they present meaningful upside, they also introduce a new category of governance and security risk that most enterprises are not yet prepared to manage. And as a CIO or CTO, you need to act now.
Consider a simple example: an agent connects to your email, CRM, and collaboration platforms, then it triages a customer’s inbound request, drafts and sends a response, updates records in the CRM, and flags exceptions. What once took hours or days can now happen in minutes. It’s easier than ever to become a 24x7x365 operation.
Those same capabilities create new risk in ways that traditional governance models don’t account for.
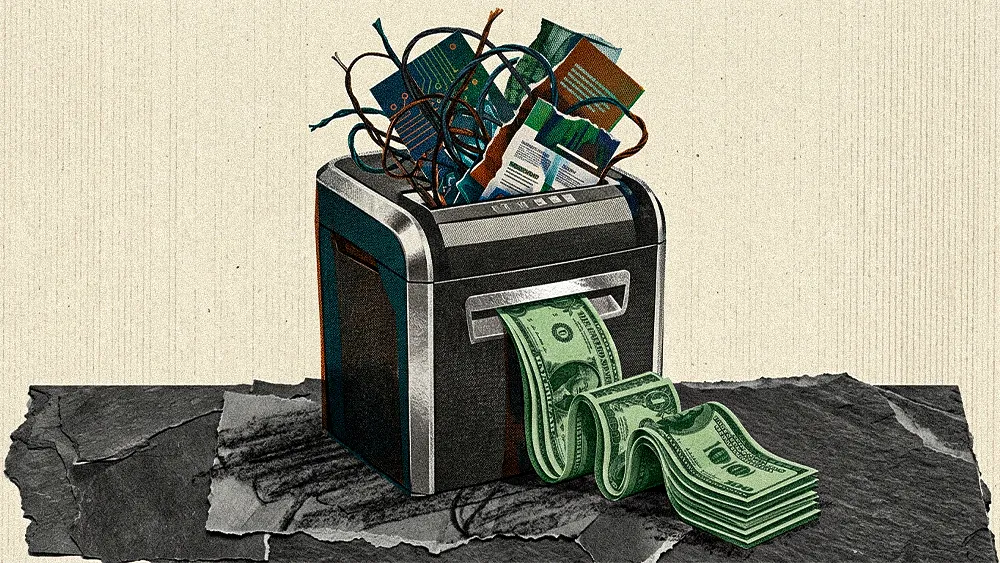
- Execution risk: Today’s IT and Security leaders are well-versed on data leakage from human employees, but not AI agents. An agent can send emails, update systems, or make decisions based on incomplete or even wrong context. Or, a misconfigured agent could communicate incorrect pricing to a customer or trigger unintended transactions. Data exposure is no longer the only concern. Agents take action, and they do it at scale.
- Identity and accountability gaps: Accountability for agent actions is unclear. Is it the employee who deployed the agent, the system it accessed or the platform that served the model? And the question of whether employees are authorized to share their credentials with agentic systems remains unsettled, with breach risk attached. Most IAM models are not designed for non-human actors operating dynamically across systems. Without clear attribution, auditability breaks down.
- Shadow AI labor: Call this shadow workforce. It's a different problem than shadow IT, because the agents do the work. Employees are already creating personal agents to automate parts of their job. When that employee leaves or moves teams, the agent often stays. The enterprise didn’t hire that agent, but it now depends on it.
- Costs: This is also driving huge, unplanned and invisible cost increases in both direct and indirect token usage. Compute, API’s and storage are just three examples of where runaway costs can quickly add up. Without governance and observability into agent activity, this can quickly lead to a new type of shadow infrastructure spend that a CIO will be responsible for solving.
- Observability and compliance challenges: When an agent approves a claim, rejects a customer, or recommends terms, you need to be able to reconstruct why. In some regulated industries like finance, that’s not optional. Without clear logs and traceability, organizations expose themselves to regulatory and legal risk.
Perhaps one of the biggest misconceptions is that organizations can simply layer AI agents onto existing enterprise architectures without significant change. Most enterprise environments were designed around human users interacting with systems in (mostly) predictable ways. AI agents fundamentally disrupt that model. The focus needs to be on redesigning the architectural layers between agents and the systems they touch. The control plane is the layer responsible for governance, identity, and policy enforcement. It’s where my recommendations below on RBAC, observability, and logging will sit.
This is not a future problem. It’s already here, and your employees are using these tools with or without your permission. Your job is to shape adoption. You have an obligation to provide pragmatic tools and processes to help safely enable the enterprise. CIO’s should take five immediate actions:
- Establish a digital labor policy: Move beyond generic “AI policies.” Work with leaders like your CHRO to define what agents are allowed to do, where human oversight is required, and which systems are off-limits. Be explicit about execution boundaries. And ensure you have a leadership governance structure in place that regularly evaluates this, as capabilities and opportunities are rapidly evolving.
- Invest in education: Employees will use these tools regardless. Acknowledge the benefits, but clearly communicate risks. Create a “safe harbor” environment where teams can experiment within defined guardrails, rather than pushing usage underground.
- Implement role-based controls for agents: Extend role-based access controls to non-human actors. Give agents scoped, purpose-specific permissions tied to their function. They should not inherit the full access of the user who deployed them. Ensure each agent has its own verifiable identity & cryptographic ID. New approaches that issue agents their own verifiable identities are emerging across the major cloud and security platforms.
- Build observability and logging: You must be able to answer simple questions, such as “What did the agent do? When and why?” Logging needs to evolve from access tracking to execution tracking.
- Partner strategically with vendors: Engage your key technology partners. Understand how they are embedding agents into their platforms and what governance capabilities they provide. Workday, SAP, Oracle, Cisco and hundreds of other software and hardware manufacturers are facing these same problems and have the resources to help create solutions. This ecosystem is evolving rapidly.
CIOs don’t need to start from scratch. Established frameworks like the National Institute of Standards and Technology (NIST) provide a strong foundation, particularly around risk management, identity, and controls. These frameworks help structure thinking, align stakeholders, and accelerate internal buy-in across security, legal, and business teams. Frameworks won’t solve the problem, but they may help you solve it inconsistently.
Cowork agents are a fundamental shift in how work gets done. None of this is optional anymore. Building trust into digital coworkers early is how you scale without sacrificing control, and how you stay ahead of the governance problem instead of cleaning it up later.
Todd Mazza is the former CTO of Factory Mutual Insurance Company. He’s also held leadership roles at Rockwell Automation, Workday, AECOM, Levi Strauss & Co, MGM Mirage and NBC Universal. Contact Todd: LinkedIn | @ToddMazzaCIO on X
.svg)